News & Events
- Beware of Fake Auto Dealer Scams
Law enforcement agencies nationwide are warning consumers about a growing auto fraud scheme targeting car buyers online. Scammers are posing as legitimate dealerships and luring buyers with attractive vehicle listings—often for cars that don’t actually exist.
- VISA FIFA World Cup 2026 Sweepstakes
Ever dreamed of seeing the FIFA WORLD CUP 26™ live?
Use a participating bank or financial organization eligible Visa Card between 02/01/2026 – 03/31/2026 and you could win a trip for two. For all participating bank and financial organization eligible Visa cards.
- Souper Bowl of Caring 2026
That’s a wrap on our 2026 Souper Bowl of Caring campaign!
For the third year in a row, we were proud to partner with Sinclair Broadcasting Group and Tackle Hunger to support our local community through the Souper Bowl of Caring initiative.
- U1 Holiday Newsletter 2025
HOLIDAY NEWSLETTER 2025
- Annual Meeting & eProxy
- Holiday Helper
- 2026 Glen R Kershner Memorial Scholarship
- Protect Yourself From Phone Spoofing Scams
- Save Money and Win Tax Season
- Beavercreek Renovations
- Holiday Schedule
- U1 Music Series at Dayton Live
- Stebbins & Fairborn High Schools Step Up For Unity Blood Drive
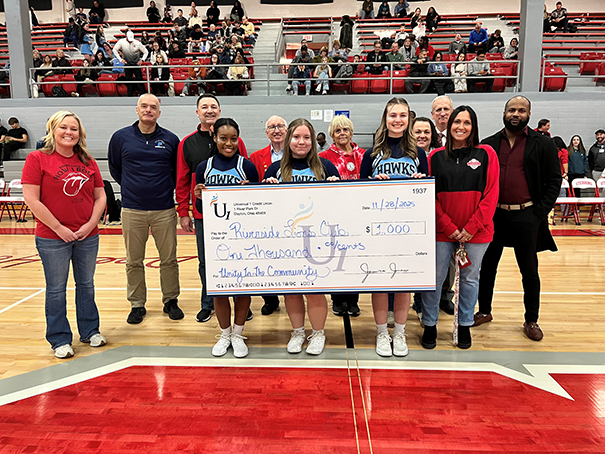
RIVERSIDE, Ohio – Stebbins High School wrapped up the seventh annual Unity in the Community campaign with rival Fairborn High School by hosting its Unity Blood Drive.
- U1 Fall Newsletter 2025
FALL NEWSLETTER 2025
- System Upgrade FAQ & Online & Mobile Banking Tutorials
- River Park Renovations
- 2026 Annual Meeting & GBQ Partners Notice
- Holiday Hours
- U1 VIP Auto Loans
- U1 Home Remedy Loans
- Exclusive Dayton Live Ticket Giveaway
- U1 Summer Newsletter 2025
SUMMER NEWSLETTER 2025
- Home Remedy Loans
- 2025 Glen R Kershner Scholarship Winners
- AI Cybersecurity
- Shred Day
- Holiday Hours
- U1 River Park Renovation Updates
- School Supply Drive
- What our Members are Saying
- Exclusive Reds Ticket Giveaway
- Rose Music Center Calendar
- Forbes Best Credit Unions In Each State
We are proud to announce that Universal 1 Credit Union (U1) has been recognized by Forbes as one of the best credit unions in the state of Ohio. This prestigious honor reflects our ongoing commitment to excellence and to serving our members and communities.
- A Table's Tale
How a CEO saved the table used for the Dayton Peace Accords
A table on which the historic Dayton Peace Accords were signed on Wright-Patterson Air Force Base in November 1995 has found a temporary home in the Benjamin and Marian Schuster Center in downtown Dayton for the NATO Parliamentary Assembly this weekend.

- U1 Spring Newsletter 2025
SPRING NEWSLETTER 2025
- U1 VIP Auto Loans
- Welcome Home Grant
- 2025 Glen R Kershner Memorial Scholarship
- Save Money and Win Tax Season
- What Our Members are Saying
- Drive-By Downloads
- Go Red for Women
- Souper Bowl of Caring
- Unity In The Community
- Dragon Tickets Giveaway
- River Park Renovations
- Rose Music Center Calendar
- U1 Holiday Newsletter 2024
HOLIDAY NEWSLETTER 2024
- A Special Note From The President/CEO
- 2025 Annual Meeting
- 2025 Glen R Kershner Memorial Scholarship
- Renovation Updates
- Winter Wonder Loan
- Save Money and Win Tax Season
- How To Pay Off Credit Card Debt
- Discover How To Afford A Mortgage In 2024
- Upcoming Holiday Closings
- Upcoming U1 Music Series Shows
- Kettering Fairmont High Unity Blood Drive
KETTERING, Ohio – Fairmont High School Kicked off the milestone 10th annual Unity in the Community Campaign with its"Unity Blood Drive" on Oct. 10.
It was not only the biggest Solvita high school blood drive of the fall, but it was also Fairmont’s biggest Unity Blood Drive turnout since before the COVID 19 pandemic, and it completed a blockbuster fall of achievement for Fairmont’s United Student Body.


